It feels like daily we see headlines of a new ransomware attack. Even if you’re not diligently staying on top of cybersecurity news, it’s hard to deny that the scope and frequency of these attacks are increasing.
In 2021 alone, we witnessed major incidents with an oil pipeline, a meat processing facility and a managed-service provider–all experiencing massive data breaches. If it seems like there have been more attacks lately, it’s because there have been. According to Blackfog’s State of Ransomware tracker, each month of 2021 has seen more attacks than it’s 2020 predecessor.
Given the enormous spike in cyber attacks, we recently held a roundtable on the topic with security experts from our enterprise network. Our goal was simple: to learn how to “deal” with the current ransomware problem, whether that meant prevention, preparation or mitigation.
What we learned from the group, which included executives from organizations like Secureworks, AEG, Netskope, Harrods, the FBI and others, was that ransomware should be treated as an expected problem. In other words, enterprises should think that it will happen to them. It’s not a question of if, but when.
Attacks are Becoming More Sophisticated
As the prevalence of these attacks has increased, we’ve seen a small change in the type of attacks taking place. Historically, system intrusions were encryption-oriented. Meaning, a set of systems would be encrypted with a private key that, upon payment of the ransom, would be released to the victim.
We are now seeing another, more public type of ransomware becoming popular, dubbed the “name-and-shame” attack. This type of intrusion is considered double-extortion as the victim is not only compromised, but the attacker also threatens to release the acquired, confidential information publicly. Due to the ever-growing interest in these attacks, this “public shaming” serves to cause reputational damage to companies, which no amount of paid ransom can recover. The bigger the target in these situations, the larger the ransom–due to implications on stock price, customer loyalty, regulatory bodies and so on.
We also learned in our roundtable that it’s now possible for attackers to be inside a victim’s systems for much longer before announcing their presence. This “patience” is caused by a change in mindset of attackers; they now see more value in the information within systems versus simply the fact that systems are breached. Rather than announcing their presence upon entry, hackers are able to stay quiet while they browse a company’s system for the best source of data.
Prevention Is and Always Has Been Key
On the top of every CISO’s mind is prevention. That is the gold-standard mindset of any good security professional: how do you protect against intrusion. In speaking with top security leaders, we uncovered attacks can happen one of three ways:
- By scanning and exploiting public systems
- By stealing employee credentials
- Via commodity software installations
The solutions to these attack vectors are quite straightforward and have been in practice for years, though to varying degrees of thoroughness:
- Patch all systems and conduct regular penetration testing
- Deploy multi-factor authentication as a majority of attacks are currently via social engineering
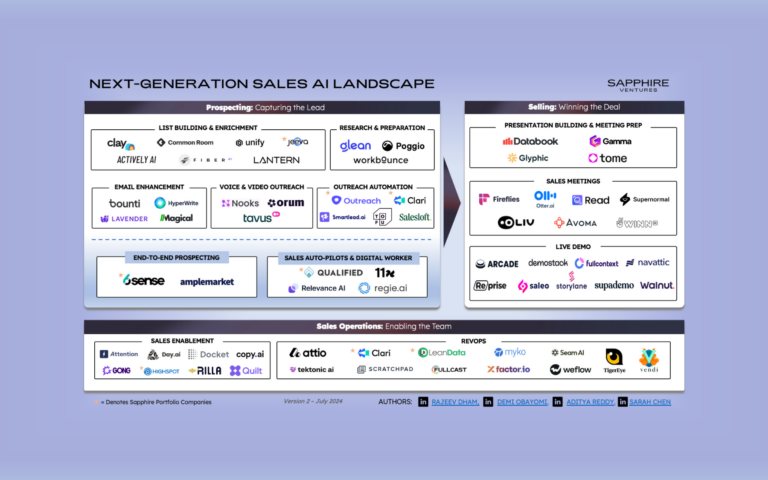
- Deploy network and endpoint detection solutions (via Sapphire portfolio companies Netskope and Exabeam, for instance)
- Employ a zero-trust framework
- Utilize data governance and analytics solutions (Sapphire portfolio companies Privacera and Uptycs can help here)
- Create an incident response plan
- Practice good digital-asset management (consider Sapphire portfolio company Jupiter One to help in this area)
On that note, it’s worth highlighting that a big and important lesson came out of the attack on Kaseya in July 2021. If you deploy a MSP, you might not be in control of all your systems. Make sure your third-party providers stick to the same rigor that you do for security.
Coming out of the roundtable, a quote stuck with us in this conversation:
“Think that you are 3 to 5 years behind the criminals. Your goal is to be better than the next target on their list, so they find getting into your systems just beyond their level of effort.”
Strategies for Staying Prepared
Preparing for an attack has many facets, especially since each attack is different than the other, so we’ve distilled it into a few key points to consider:
- Stress-test your response: There’s no way to really be ready for the day of an attack, as most executives agreed that “your IQ drops 20 points when in real-response mode.” So the best way to prep is to:
- Create an incident response plan and put together tabletop exercises for your team to get familiar with protocol
- “Bring down” any systems you can to do hands-on training
- Learn the basics of isolation and containment.
- Prepare the business: Our current IT expectation is one of efficiency. The business should know that, in the event of an attack, efficiency will be de-prioritized. Business systems will be down and backups will be in play. Know the efficiency of your backup and what percentage is quick to recover. Regularly test your offline recovery to give a likely scenario to the business for an attack.
- Your non-IT response: In your incident response plan, you should have critical mass points. When X happens, what is the corresponding Y action? Know the basic services that you can have available if you need to take your system down. Prepare your marketing and PR teams with a ransomware toolkit. And know which law enforcement agencies you’ll need to contact.

We reached out to the team at the FBI who joined our roundtable for their take on further steps for preparedness. According to San Francisco FBI Assistant Special Agent in Charge Elvis Chan:
“Given the current crescendo of ransomware and supply chain attacks, I have three pieces of advice for companies:
- Reach out now and establish a relationship with your local FBI field office. As a victim, you don’t want your first phone call to the FBI on a Friday night when your networks are locked out and your hair is on fire.
- Your company should implement multi-factor authentication in order to access your corporate email accounts and networks. A significant portion of the cyberattacks we observe involve brute force attacks, such as password spraying.
- In the longer term, you should work toward implementing a “zero trust” network architecture. This will involve prioritizing the most valuable data within a company and hardening them within the network.”
Recovery Options are Limited at Best
Insurance on ransomware resolution is booming at the moment, but perhaps too fast for some creditors. With the frequency of attacks, premiums are increasing, even leading to “co-insurance payment” structures where both the insurers and victims are on the hook for payment. Speak to your legal team and understand if you have a contractual obligation for insurance. If not, the price of cyber insurance is likely not worth the coverage at the moment.
The most obvious resolution to a ransomware attack is to pay the ransom. Gain the key to decrypt, fix up your systems and move on. Take the Colonial Pipeline incident as an example. Payment was their way out. And lucky for them, the U.S. government was able to recover nearly half what they paid, but this is very much the exception to the norm.
Payment is a dangerous and increasingly unpopular option, which further perpetuates the attractiveness of cyber attacks for these criminals. Furthermore, late last year, the U.S. Treasury indicated that there may be major legal implications to paying any ransom that originates from a sanctioned country.
The Rub
We wish we had better news. It doesn’t appear that the public ransomware problem is going away anytime soon. With attackers becoming more emboldened and going after larger targets, there is a sense of foreboding that many CISOs have. Through our conversations with the executives at our roundtable, the advice is simply to hope for the best, practice proper cyber hygiene and security posture management, but prepare for the worst. Regularly updating and checking internal and external systems might seem like a tall task amidst the hundreds of other priorities, but close alignment with overall leadership (CEO, CIO, etc.) is the first step to normalizing a secure company framework.